They can steal your smartcard, lift your passport, jack your car, even clone the chip in your arm. And you won't feel a thing. 5 tales from the RFID-hacking underground.
James Van Bokkelen is about to be robbed. A wealthy software entrepreneur, Van Bokkelen will be the latest victim of some punk with a laptop. But this won't be an email scam or bank account hack. A skinny 23-year-old named Jonathan Westhues plans to use a cheap, homemade USB device to swipe the office key out of Van Bokkelen's back pocket.
"I just need to bump into James and get my hand within a few inches of him," Westhues says. We're shivering in the early spring air outside the offices of Sandstorm, the Internet security company Van Bokkelen runs north of Boston. As Van Bokkelen approaches from the parking lot, Westhues brushes past him. A coil of copper wire flashes briefly in Westhues' palm, then disappears.
Van Bokkelen enters the building, and Westhues returns to me. "Let's see if I've got his keys," he says, meaning the signal from Van Bokkelen's smartcard badge. The card contains an RFID sensor chip, which emits a short burst of radio waves when activated by the reader next to Sandstorm's door. If the signal translates into an authorized ID number, the door unlocks.
The coil in Westhues' hand is the antenna for the wallet-sized device he calls a cloner, which is currently shoved up his sleeve. The cloner can elicit, record, and mimic signals from smartcard RFID chips. Westhues takes out the device and, using a USB cable, connects it to his laptop and downloads the data from Van Bokkelen's card for processing. Then, satisfied that he has retrieved the code, Westhues switches the cloner from Record mode to Emit. We head to the locked door.
"Want me to let you in?" Westhues asks. I nod.
He waves the cloner's antenna in front of a black box attached to the wall. The single red LED blinks green. The lock clicks. We walk in and find Van Bokkelen waiting.
"See? I just broke into your office!" Westhues says gleefully. "It's so simple." Van Bokkelen, who arranged the robbery "just to see how it works," stares at the antenna in Westhues' hand. He knows that Westhues could have performed his wireless pickpocket maneuver and then returned with the cloner after hours. Westhues could have walked off with tens of thousands of dollars' worth of computer equipment - and possibly source code worth even more. Van Bokkelen mutters, "I always thought this might be a lousy security system."
RFID chips are everywhere - companies and labs use them as access keys, Prius owners use them to start their cars, and retail giants like Wal-Mart have deployed them as inventory tracking devices. Drug manufacturers like Pfizer rely on chips to track pharmaceuticals. The tags are also about to get a lot more personal: Next-gen US passports and credit cards will contain RFIDs, and the medical industry is exploring the use of implantable chips to manage patients. According to the RFID market analysis firm IDTechEx, the push for digital inventory tracking and personal ID systems will expand the current annual market for RFIDs from $2.7 billion to as much as $26 billion by 2016.
RFID technology dates back to World War II, when the British put radio transponders in Allied aircraft to help early radar system crews detect good guys from bad guys. The first chips were developed in research labs in the 1960s, and by the next decade the US government was using tags to electronically authorize trucks coming into Los Alamos National Laboratory and other secure facilities. Commercialized chips became widely available in the '80s, and RFID tags were being used to track difficult-to-manage property like farm animals and railroad cars. But over the last few years, the market for RFIDs has exploded, driven by advances in computer databases and declining chip prices. Now dozens of companies, from Motorola to Philips to Texas Instruments, manufacture the chips.
The tags work by broadcasting a few bits of information to specialized electronic readers. Most commercial RFID chips are passive emitters, which means they have no onboard battery: They send a signal only when a reader powers them with a squirt of electrons. Once juiced, these chips broadcast their signal indiscriminately within a certain range, usually a few inches to a few feet. Active emitter chips with internal power can send signals hundreds of feet; these are used in the automatic toll-paying devices (with names like FasTrak and E-ZPass) that sit on car dashboards, pinging tollgates as autos whiz through.
For protection, RFID signals can be encrypted. The chips that will go into US passports, for example, will likely be coded to make it difficult for unauthorized readers to retrieve their onboard information (which will include a person's name, age, nationality, and photo). But most commercial RFID tags don't include security, which is expensive: A typical passive RFID chip costs about a quarter, whereas one with encryption capabilities runs about $5. It's just not cost-effective for your average office building to invest in secure chips.
This leaves most RFIDs vulnerable to cloning or - if the chip has a writable memory area, as many do - data tampering. Chips that track product shipments or expensive equipment, for example, often contain pricing and item information. These writable areas can be locked, but often they aren't, because the companies using RFIDs don't know how the chips work or because the data fields need to be updated frequently. Either way, these chips are open to hacking.
"The world of RFID is like the Internet in its early stages," says Ari Juels, research manager at the high tech security firm RSA Labs. "Nobody thought about building security features into the Internet in advance, and now we're paying for it in viruses and other attacks. We're likely to see the same thing with RFIDs."
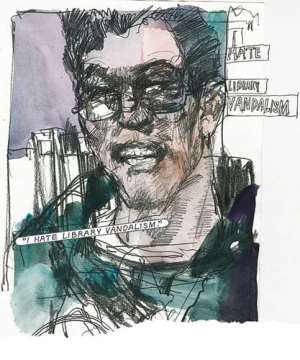
David Molnar is a soft-spoken computer science graduate student who studies commercial uses for RFIDs at UC Berkeley. I meet him in a quiet branch of the Oakland Public Library, which, like many modern libraries, tracks most of its inventory with RFID tags glued inside the covers of its books. These tags, made by Libramation, contain several writable memory "pages" that store the books' barcodes and loan status.



 Tuesday’s downpour destroys ceiling of Circuit Court '8' in Accra
Tuesday’s downpour destroys ceiling of Circuit Court '8' in Accra
 SOEs shouldn't compromise on ethical standards, accountability – Akufo-Addo
SOEs shouldn't compromise on ethical standards, accountability – Akufo-Addo
 Father of 2-year-old boy attacked by dog appeals for financial support
Father of 2-year-old boy attacked by dog appeals for financial support
 Jubilee House National Security Operative allegedly swindles businessman over sa...
Jubilee House National Security Operative allegedly swindles businessman over sa...
 Nobody can order dumsor timetable except Energy Minister – Osafo-Maafo
Nobody can order dumsor timetable except Energy Minister – Osafo-Maafo
 Mahama wishes National Chief Imam as he clock 105 years today
Mahama wishes National Chief Imam as he clock 105 years today
 J.B.Danquah Adu’s murder trial: Case adjourned to April 29
J.B.Danquah Adu’s murder trial: Case adjourned to April 29
 High Court issues arrest warrant for former MASLOC Boss
High Court issues arrest warrant for former MASLOC Boss
 Align academic curriculum with industry needs — Stanbic Bank Ghana CEO advocates
Align academic curriculum with industry needs — Stanbic Bank Ghana CEO advocates
 Election 2024: We'll declare the results and let Ghanaians know we've won - Manh...
Election 2024: We'll declare the results and let Ghanaians know we've won - Manh...
